You need to grant a user a named User1 access to download compliance reports from the Security & Compliance reports from the Security from the Security & Compliance admin center. The solution must use the principle of least privilege.
What should you do?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals- Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You discover that some external users accessed content on a Microsoft SharePoint site. You modify the SharePoint sharing policy to prevent sharing outside your organization.
You need to be notified if the SharePoint sharing policy is modified in the future.
Solution: From the Security & Compliance admin center, you create a threat management policy.
Does this meet the goal?
You have a Microsoft 365 E5 tenant.
You configure sensitivity labels.
Users report that the Sensitivity button is unavailability in Microsoft Word for the web. The sensitivity button is available in Word for Microsoft 365.
You need to ensure that the users can apply the sensitivity labels when they use Word for the web.
What should you do?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals- Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
You discover that some external users accessed content on a Microsoft SharePoint site. You modify the SharePoint shoring policy to prevent sharing outside your organization.
You need to be notified if the SharePoint sharing policy is modified m the future.
Solution: From the SharePoint site, you create an alert.
Does this meet the goal?
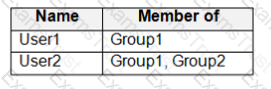
You have a Microsoft 365 subscription that uses a default domain named contoso.com. The domain contains the users shown in the following table.
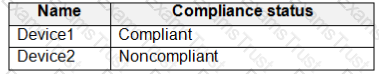
The domain contains the devices shown in the following table.
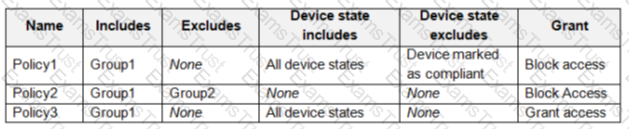
The domain contains conditional access policies that control access to a cloud app named App1. The policies are configured as shown in the following table.
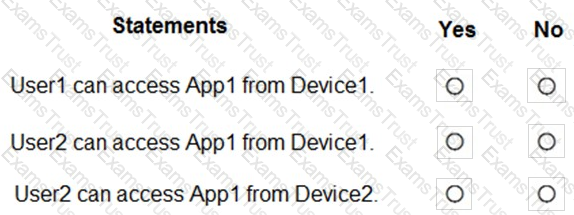
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Your company has a Microsoft 365 subscription. The subscription contains 500 devices that run Windows 10 and 100 devices that run iOS.
You need to create Microsoft Intune device configuration profiles to meet the following requirements:
* Configure Wi-Fi connectivity to a secured network named ContosoNet.
* Require passwords of at least six characters to lock the devices.
What is the minimum number of device configuration profiles that you should create?
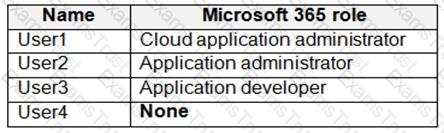
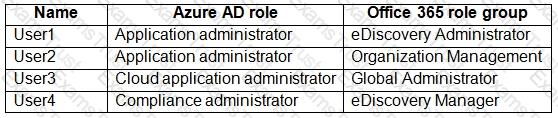
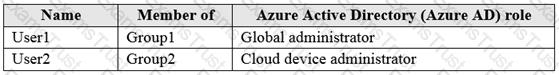
You have a Microsoft Azure Active Directory (Azure AD) tenant named Contoso.com.
You create a Microsoft Defender for identity instance Contoso.
The tenant contains the users shown in the following table.
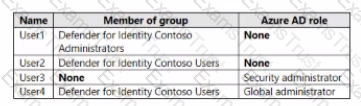
You need to modify the configuration of the Defender for identify sensors.
Solutions: You instruct User1 to modify the Defender for identity sensor configuration.
Does this meet the goal?
You have a Microsoft 365 subscription. You have a user named User1.
You need to ensure that Used can place a hold on all mailbox content.
What permission should you assign to User1?
: 161
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 subscription.
From the Security & Compliance admin center, you create a role group named US eDiscovery Managers by copying the eDiscovery Manager role group.
You need to ensure that the users in the new role group can only perform content searches of mailbox content for users in the United States.
Solution: From the Azure Active Directory admin center, you create a conditional access policy.
Does this meet the goal?
Your company has a Microsoft 365 tenant.
The company sells products online and processes credit card information.
You need to be notified if a file stored in Microsoft SharePoint Online contains credit card information. The file must be removed automatically from its current location until an administrator can review its contents.
What should you use?
: 233
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft 365 E5 subscription.
You create an account for a new security administrator named SecAdmin1.
You need to ensure that SecAdmin1 can manage Office 365 Advanced Threat Protection (ATP) settings and policies for Microsoft Teams, SharePoint, and OneDrive.
Solution: From the Microsoft 365 admin center, you assign SecAdmin1 the SharePoint admin role.
Does this meet the goal?
You have computers that run Windows 10 Enterprise and are joined to the domain.
You plan to delay the installation of new Windows builds so that the IT department can test application compatibility.
You need to prevent Windows from being updated for the next 30 days.
Which two Group Policy settings should you configure? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
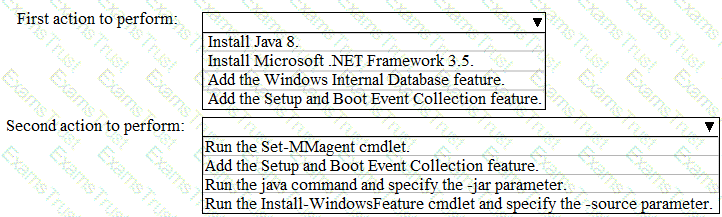
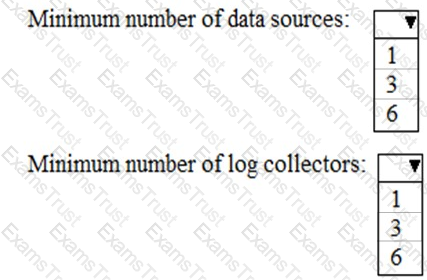
Your company uses Microsoft Cloud App Security.
You plan to integrate Cloud App Security and security information and event management (SIEM).
You need to deploy a SIEM agent on a server that runs Windows Server 2016.
What should you do? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.
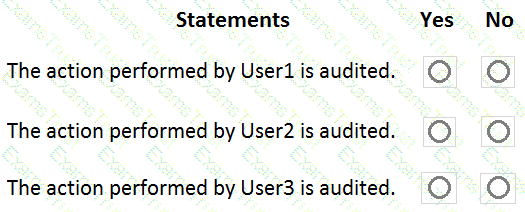
You have a Microsoft 365 subscription that contains the users shown in the following table.
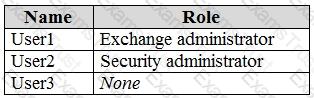
You run the following cmdlet.
Set-MailboxAuditBypassAssociation –Identity User2
–AuditByPassEnabled $true
The users perform the following actions:
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 tenant.
You plan to implement device configuration profiles in Microsoft Intune.
Which platform can you manage by using the profiles?
You have a Microsoft 365 subscription.
You are planning a threat management solution for your organization.
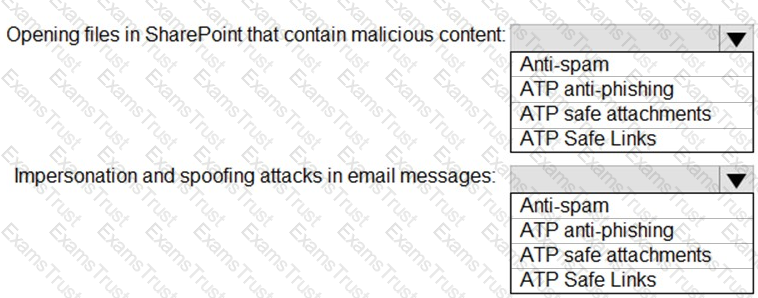
You need to minimize the likelihood that users will be affected by the following threats:
Which policies should you create in the Security & Compliance admin center? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 tenant.
The Microsoft Secure Score for the tenant is shown in the following exhibit.
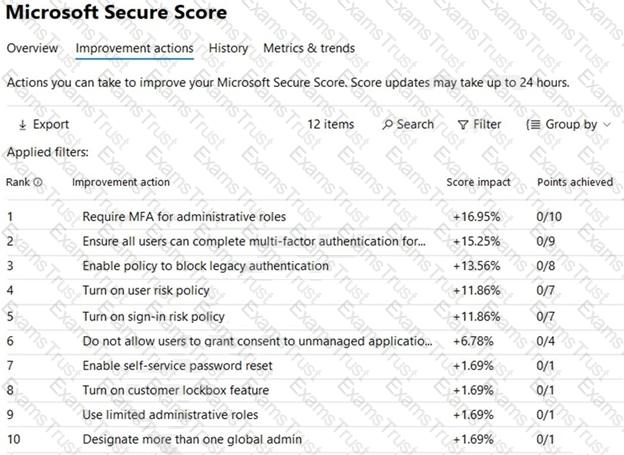
You plan to enable Security defaults for Azure Active Directory (Azure AD).
Which three improvement actions will this affect?
: 238 HOTSPOT
You have a Microsoft 365 E5 tenant that contains the users shown in the following table.
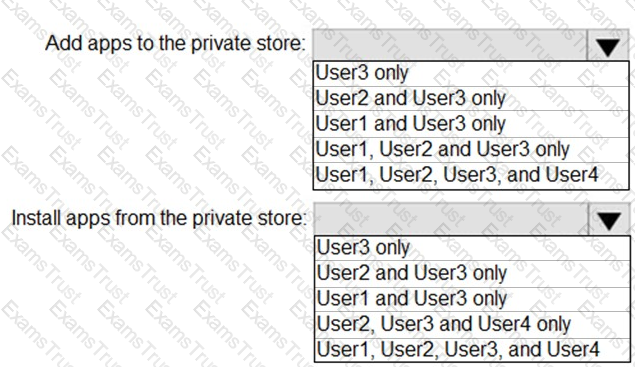
Users are assigned Microsoft Store for Business roles as shown in the following table.
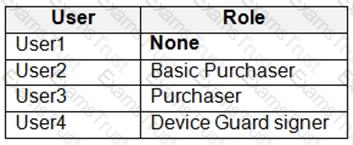
Which users can add apps to the private store in Microsoft Store for Business, and which users can install apps from the private store? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
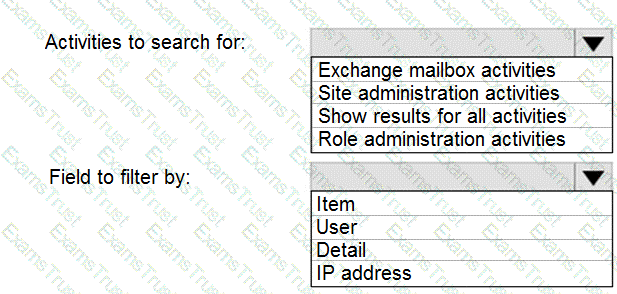
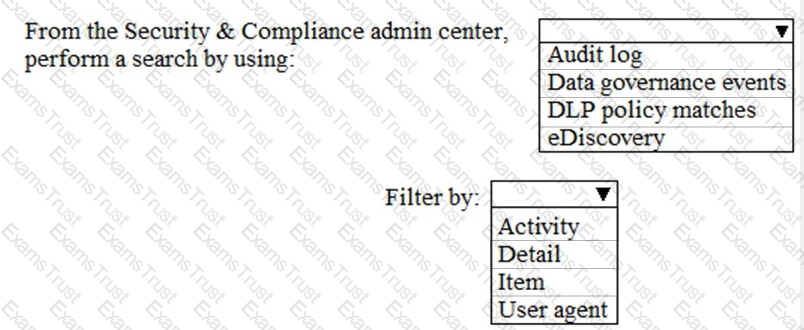
You have a Microsoft 365 subscription.
Your network uses an IP address space of 51.40.15.0/24.
An Exchange Online administrator recently created a role named Role1 from a computer on the network.
You need to identify the name of the administrator by using an audit log search.
For which activities should you search and by which field should you filter in the audit log search? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 tenant.
You create a retention label as shown in the Retention Label exhibit. (Click the Retention Label tab.)
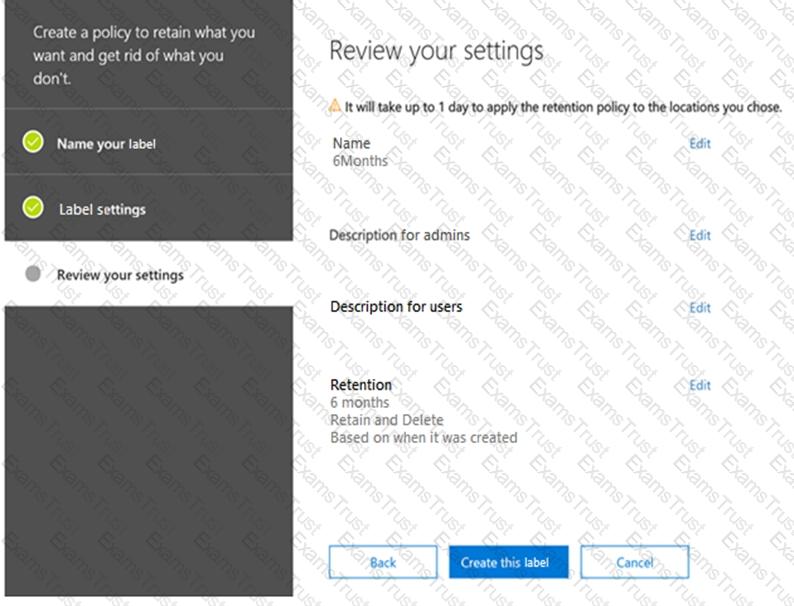
You create a label policy as shown in the Label Policy Exhibit. (Click the Label Policy tab.)
The label policy is configured as shown in the following table.
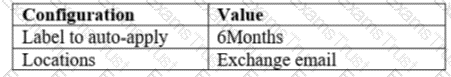
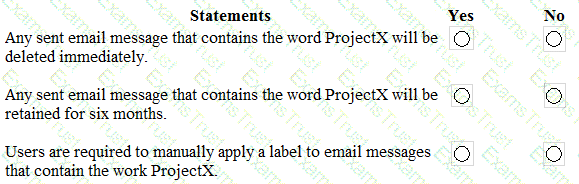
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
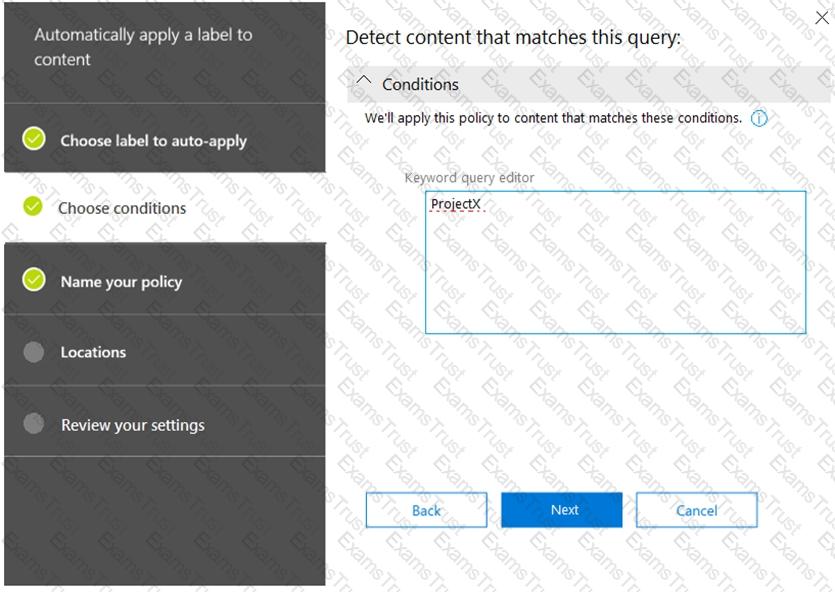
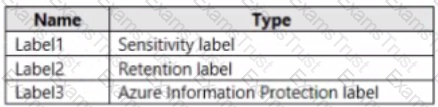
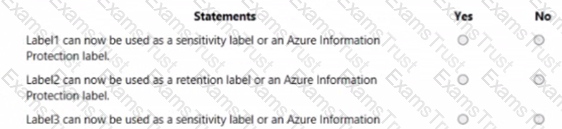
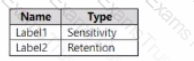
Your company has a Microsoft 365 subscription that uses an Azure Active Directory (Azure AD) tenant named contoso.com. The company stores 2 TBs of data in SharePoint Online document libraries. The tenant has the labels shown in the following table.
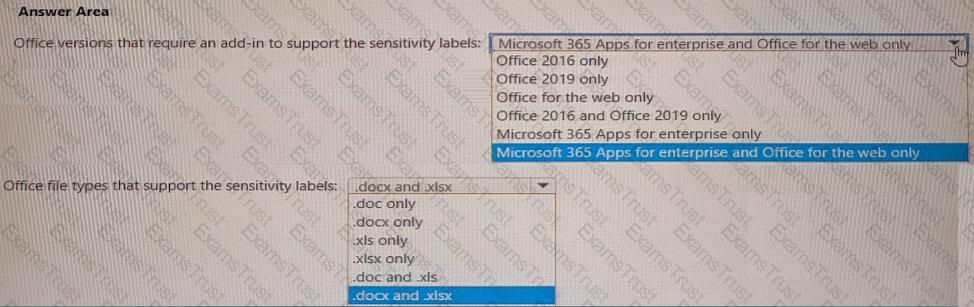
Your company has a Microsoft 365 E5 tenant.
Users at the company use the following versions of Microsoft Office:
• Microsoft 365 Apps for enterprise
• Office for the web
• Office 2016
• Office 2019
The company currently uses the following Office file types:
• .docx
• .xlsx
• .doc
• xls
You plan to use sensitivity labels. You need to identify the following:
• Which versions of Office require an add-in to support the sensitivity labels.
• Which file types support the sensitivity labels.
What should you identify? To answer, select the appropriate options in the answer area, NOTE: Each correct selection is worth one point.
You have a Microsoft 365 tenant that contains two users named User1 and User2. You create the alert policy shown in the following exhibit.
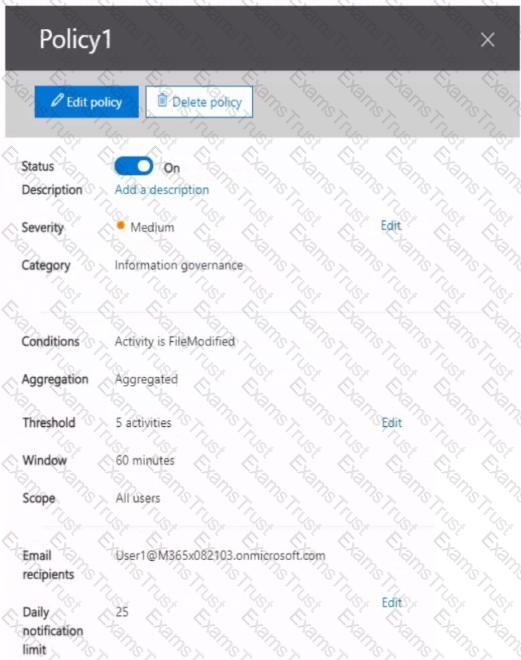
User2 runs a script that modifies a file in a Microsoft SharePoint Online library once every four minutes and runs for a period of two hours.
How many alerts will User1 receive?
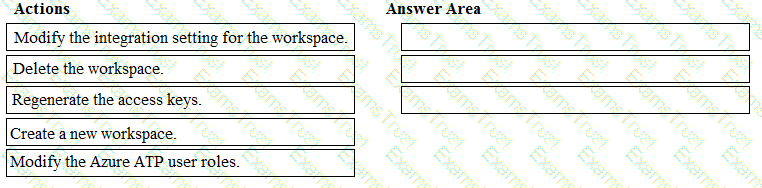
You have the Microsoft Azure Advanced Threat Protection (ATP) workspace shown in the Workspace exhibit. (Click the Workspace tab.)
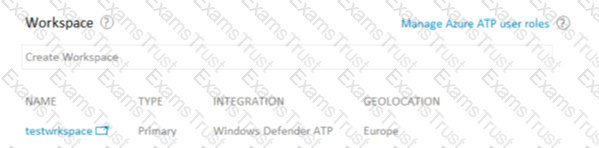
The sensors settings for the workspace are configured as shown in the Sensors exhibit. (Click the Sensors tab.)

You need to ensure that Azure ATP stores data in Asia.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You have a Microsoft 365 E5 subscription that contains the labels shown in the following table.
You have the items shown in the following table.
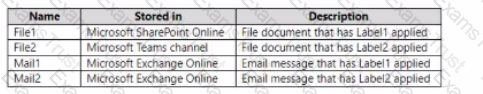
Which items can you view in Content explorer?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a computer that runs Windows 10.
You need to verify which version of Windows 10 is installed.
Solution: At a command prompt, you run the winver.exe command.
Does this meet the goal?
: 158 HOTSPOT
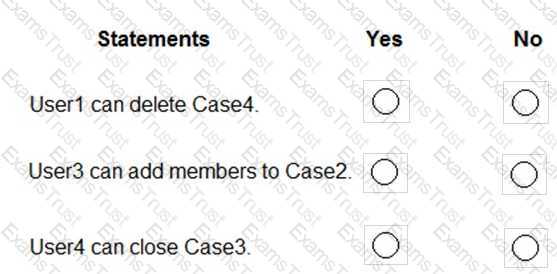
You have a Microsoft 365 tenant named contoso.com. The tenant contains the users shown in the following table.
You have the eDiscovery cases shown in the following table.
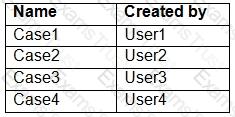
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
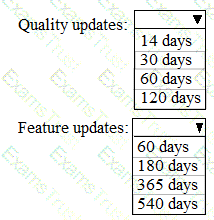
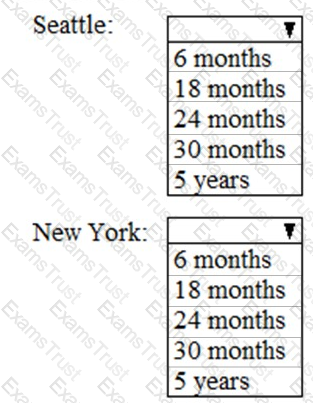
Your network contains an Active Directory domain named contoso.com. All client devices run Windows 10 and are joined to the domain.
You update the Windows 10 devices by using Windows Update for Business.
What is the maximum amount of time you can defer Windows 10 updates? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that contains the users shown in the following table.
You configure an Enrollment Status Page profile as shown in the following exhibit.
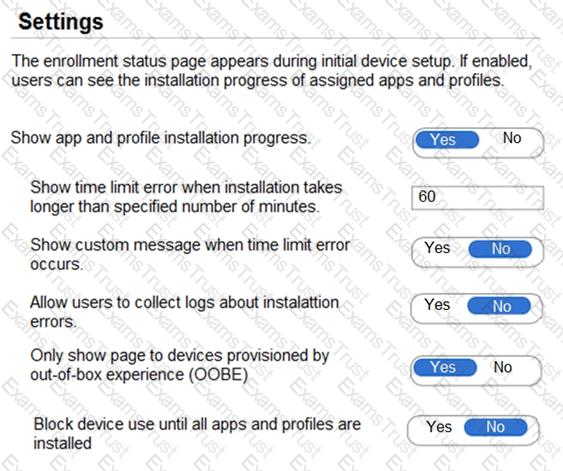
You assign the policy to Group1.
You purchase the devices shown in the following table.
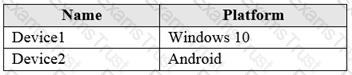
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
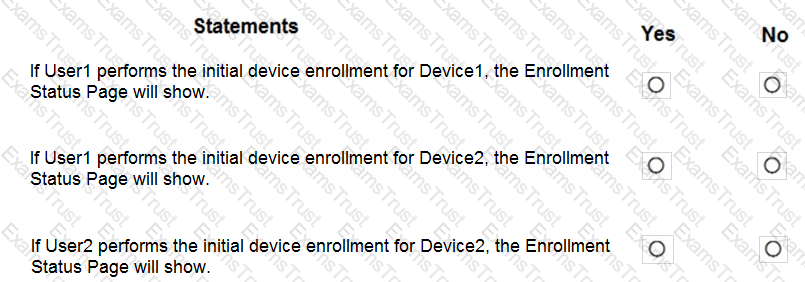
You have a Microsoft 365 E5 tenant that contains two users named User1 and User2 and the groups shown in the following table.
You have a Microsoft Intune enrollment policy that has the following settings:
You purchase the devices shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
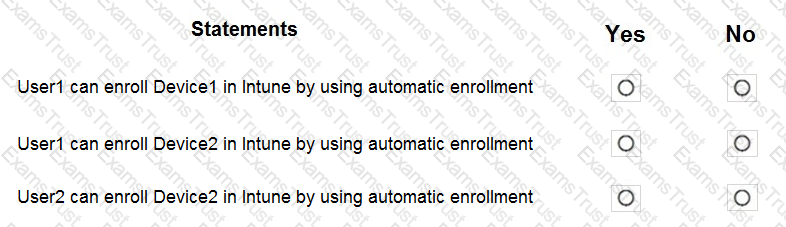
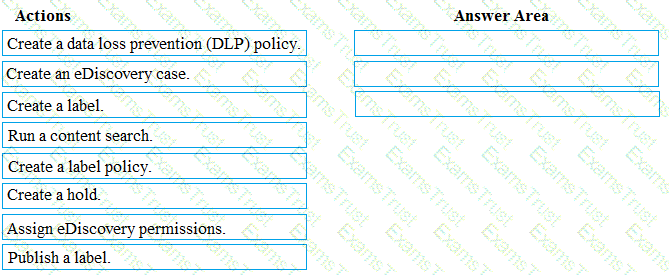
You need to meet the requirement for the legal department.
Which three actions should you perform in sequence from the Security & Compliance admin center? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to meet the technical requirement for the EU PII data.
What should you create?
You need to protect the U.S. PII data to meet the technical requirements.
What should you create?
You need to recommend a solution for the security administrator. The solution must meet the technical requirements.
What should you include in the recommendation?
You need to meet the technical requirement for the SharePoint administrator. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Which report should the New York office auditors view?
You need to meet the technical requirement for log analysis.
What is the minimum number of data sources and log collectors you should create from Microsoft Cloud App Security? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the technical requirement for large-volume document retrieval. What should you create?
On which server should you use the Defender for identity sensor?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com that is synced to Microsoft Azure Active Directory (Azure AD).
You manage Windows 10 devices by using Microsoft System Center Configuration Manager (Current Branch).
You configure a pilot for co-management.
You add a new device named Device1 to the domain. You install the Configuration Manager client on Device1.
You need to ensure that you can manage Device1 by using Microsoft Intune and Configuration Manager.
Solution: You create a device configuration profile from the Device Management admin center.
Does this meet the goal?
You need to ensure that User1 can enroll the devices to meet the technical requirements. What should you do?
You need to create the Microsoft Store for Business. Which user can create the store?
You need to ensure that the support technicians can meet the technical requirement for the Montreal office mobile devices.
What is the minimum of dedicated support technicians required?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com that is synced to Microsoft Azure Active Directory (Azure AD).
You manage Windows 10 devices by using Microsoft System Center Configuration Manager (Current Branch).
You configure a pilot for co-management.
You add a new device named Device1 to the domain. You install the Configuration Manager client on Device1.
You need to ensure that you can manage Device1 by using Microsoft Intune and Configuration Manager.
Solution: Define a Configuration Manager device collection as the pilot collection. Add Device1 to the collection.
Does this meet the goal?
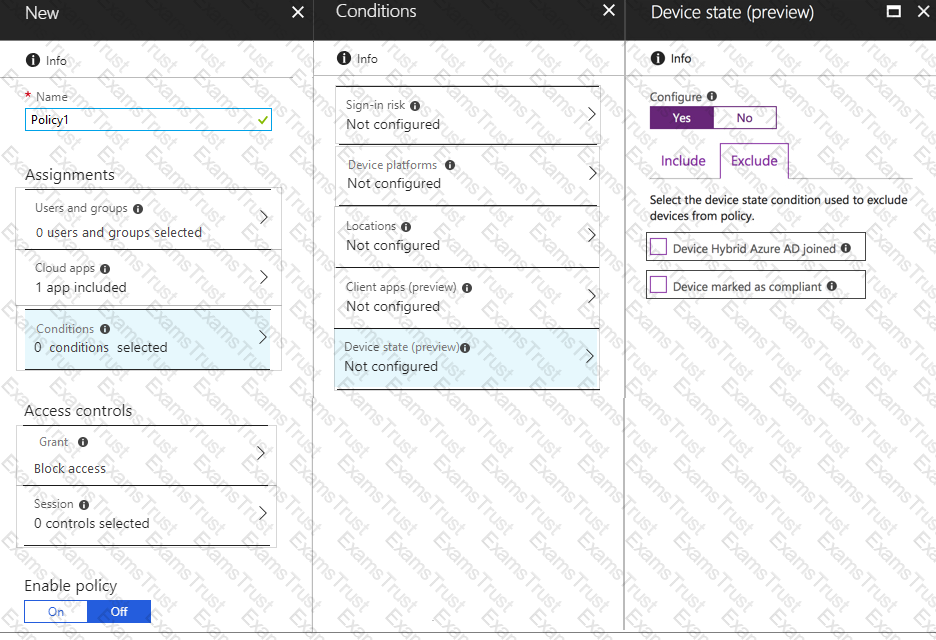
You need to configure a conditional access policy to meet the compliance requirements.
You add Exchange Online as a cloud app.
Which two additional settings should you configure in Policy1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
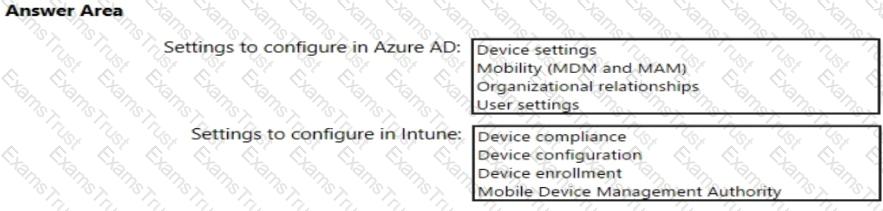
You need to meet the Intune requirements for the Windows 10 devices.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
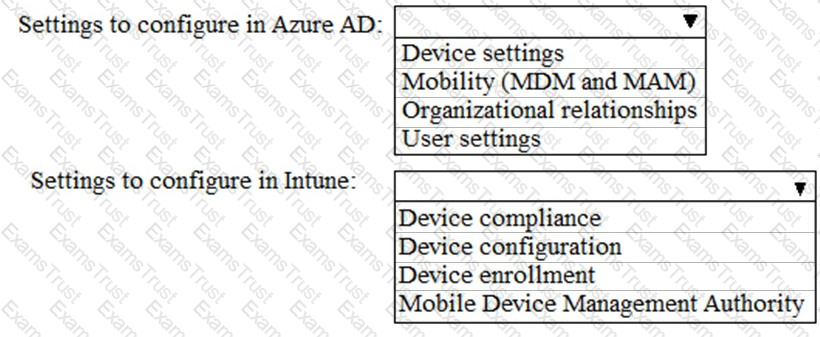
You need to meet the technical requirements and planned changes for Intune.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
As of March, how long will the computers in each office remain supported by Microsoft? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the compliance requirements for the Windows 10 devices.
What should you create from the Intune admin center?
On which server should you install the Azure ATP sensor?
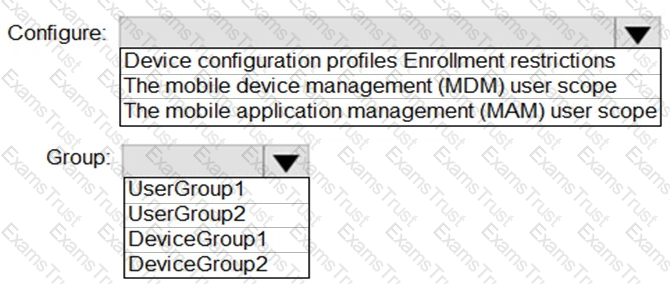
You need to configure automatic enrollment in Intune. The solution must meet the technical requirements.
What should you configure, and to which group should you assign the configurations? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure Office on the web to meet the technical requirements.
What should you do?
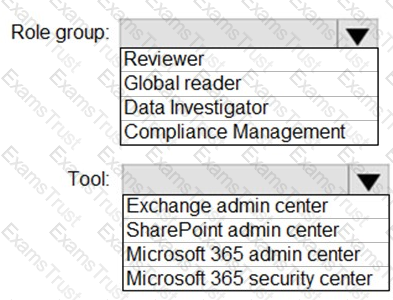
You need to ensure that User2 can review the audit logs. The solutions must meet the technical requirements.
To which role group should you add User2, and what should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You create the planned DLP policies.
You need to configure notifications to meet the technical requirements.
What should you do?
You need to create the Safe Attachments policy to meet the technical requirements.
Which option should you select?
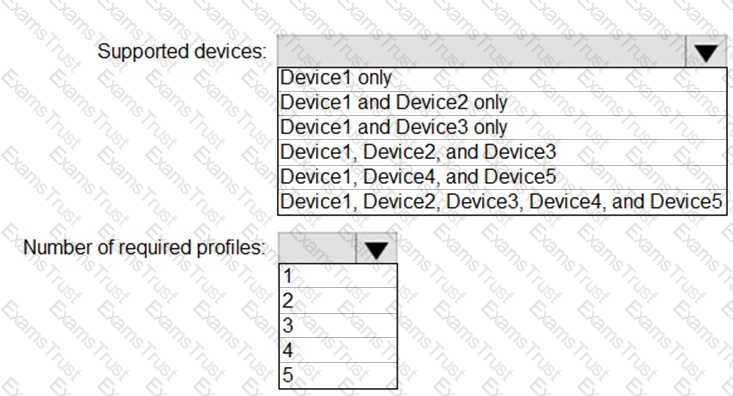
You plan to implement the endpoint protection device configuration profiles to support the planned changes.
You need to identify which devices will be supported, and how many profiles you should implement.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to create the DLP policy to meet the technical requirements.
What should you configure first?
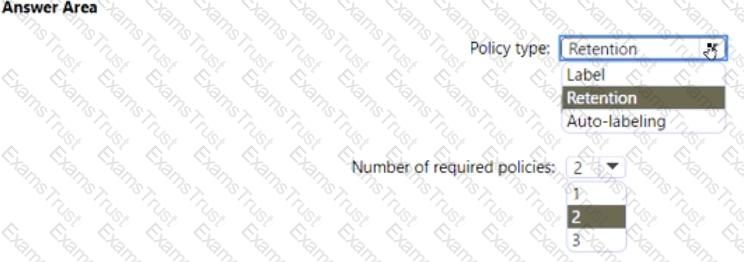
You need to configure the information governance settings to meet the technical requirements.
Which type of policy should you configure, and how many policies should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure the compliance settings to meet the technical requirements.
What should you do in the Microsoft Endpoint Manager admin center?