A vendor has been collecting data under an old contract, not aligned with the practices of the organization.
Which is the preferred response?
A valid argument against data minimization is that it?
SCENARIO
Carol was a U.S.-based glassmaker who sold her work at art festivals. She kept things simple by only accepting cash and personal checks.
As business grew, Carol couldn't keep up with demand, and traveling to festivals became burdensome. Carol opened a small boutique and hired Sam to run it while she worked in the studio. Sam was a natural salesperson, and business doubled. Carol told Sam, “I don't know what you are doing, but keep doing it!"
But months later, the gift shop was in chaos. Carol realized that Sam needed help so she hired Jane, who had business expertise and could handle the back-office tasks. Sam would continue to focus on sales. Carol gave Jane a few weeks to get acquainted with the artisan craft business, and then scheduled a meeting for the three of them to discuss Jane's first impressions.
At the meeting, Carol could not wait to hear Jane's thoughts, but she was unprepared for what Jane had to say. “Carol, I know that he doesn't realize it, but some of Sam’s efforts to increase sales have put you in a vulnerable position. You are not protecting customers’ personal information like you should.”
Sam said, “I am protecting our information. I keep it in the safe with our bank deposit. It's only a list of customers’ names, addresses and phone numbers that I get from their checks before I deposit them. I contact them when you finish a piece that I think they would like. That's the only information I have! The only other thing I do is post photos and information about your work on the photo sharing site that I use with family and friends. I provide my email address and people send me their information if they want to see more of your work. Posting online really helps sales, Carol. In fact, the only complaint I hear is about having to come into the shop to make a purchase.”
Carol replied, “Jane, that doesn’t sound so bad. Could you just fix things and help us to post even more online?"
‘I can," said Jane. “But it's not quite that simple. I need to set up a new program to make sure that we follow the best practices in data management. And I am concerned for our customers. They should be able to manage how we use their personal information. We also should develop a social media strategy.”
Sam and Jane worked hard during the following year. One of the decisions they made was to contract with an outside vendor to manage online sales. At the end of the year, Carol shared some exciting news. “Sam and Jane, you have done such a great job that one of the biggest names in the glass business wants to buy us out! And Jane, they want to talk to you about merging all of our customer and vendor information with theirs beforehand."
Which regulator has jurisdiction over the shop's data management practices?
What tactic does pharming use to achieve its goal?
What is the main privacy threat posed by Radio Frequency Identification (RFID)?
Which of the following statements is true regarding software notifications and agreements?
What is the main benefit of using dummy data during software testing?
Which of the following is a privacy consideration for NOT sending large-scale SPAM type emails to a database of email addresses?
SCENARIO
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephone, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q's business model, resources are contracted as needed instead of permanently employed.
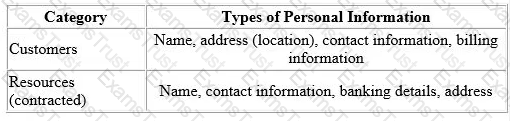
The table below indicates some of the personal information Clean-Q requires as part of its business operations:
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation. Therefore, the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q's traditional supply and demand system that has caused some overlapping bookings.
Ina business strategy session held by senior management recently, Clear-Q invited vendors to present potential solutions to their current operational issues. These vendors included Application developers and Cloud-Q’s solution providers, presenting their proposed solutions and platforms.
The Managing Director opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform: A web interface that Clean-Q accesses for the purposes of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customers to pay for services.
Which question would you most likely ask to gain more insight about LeadOps and provide practical privacy recommendations?
An organization is launching a new online subscription-based publication. As the service is not aimed at children, users are asked for their date of birth as part of the of the sign-up process. The privacy technologist suggests it may be more appropriate ask if an individual is over 18 rather than requiring they provide a date of birth. What kind of threat is the privacy technologist concerned about?
Organizations understand there are aggregation risks associated with the way the process their customer’s data. They typically include the details of this aggregation risk in a privacy notice and ask that all customers acknowledge they understand these risks and consent to the processing.
What type of risk response does this notice and consent represent?
SCENARIO
Please use the following to answer the next questions:
Your company is launching a new track and trace health app during the outbreak of a virus pandemic in the US. The developers claim the app is based on privacy by design because personal data collected was considered to ensure only necessary data is captured, users are presented with a privacy notice, and they are asked to give consent before data is shared. Users can update their consent after logging into an account, through a dedicated privacy and consent hub. This is accessible through the 'Settings' icon from any app page, then clicking 'My Preferences', and selecting 'Information Sharing and Consent' where the following choices are displayed:
• "I consent to receive notifications and infection alerts";
• "I consent to receive information on additional features or services, and new products";
• "I consent to sharing only my risk result and location information, for exposure and contact tracing purposes";
• "I consent to share my data for medical research purposes"; and
• "I consent to share my data with healthcare providers affiliated to the company".
For each choice, an ON* or OFF tab is available The default setting is ON for all
Users purchase a virus screening service for USS29 99 for themselves or others using the app The virus screening
service works as follows:
• Step 1 A photo of the user's face is taken.
• Step 2 The user measures their temperature and adds the reading in the app
• Step 3 The user is asked to read sentences so that a voice analysis can detect symptoms
• Step 4 The user is asked to answer questions on known symptoms
• Step 5 The user can input information on family members (name date of birth, citizenship, home address, phone number, email and relationship).)
The results are displayed as one of the following risk status "Low. "Medium" or "High" if the user is deemed at "Medium " or "High" risk an alert may be sent to other users and the user is Invited to seek a medical consultation and diagnostic from a healthcare provider.
A user’s risk status also feeds a world map for contact tracing purposes, where users are able to check if they have been or are in dose proximity of an infected person If a user has come in contact with another individual classified as "medium’ or 'high' risk an instant notification also alerts the user of this. The app collects location trails of every user to monitor locations visited by an infected individual Location is collected using the phone's GPS functionary, whether the app is in use or not however, the exact location of the user is "blurred' for privacy reasons Users can only see on the map circles
Which of the following is likely to be the most important issue with the choices presented in the 'Information Sharing and Consent' pages?
An organization must terminate their cloud vendor agreement immediately. What is the most secure way to delete the encrypted data stored in the cloud?
Which of the following occurs when an individual takes a specific observable action to indicate and confirm that they give permission for their information to be processed?
An organization is evaluating a number of Machine Learning (ML) solutions to help automate a customer-facing part of its business From a privacy perspective, the organization should first?
Value Sensitive Design (VSD) focuses on which of the following?
SCENARIO
WebTracker Limited is a cloud-based online marketing service located in London. Last year, WebTracker migrated its IT infrastructure to the cloud provider AmaZure, which provides SQL Databases and Artificial Intelligence services to WebTracker. The roles and responsibilities between the two companies have been formalized in a standard contract, which includes allocating the role of data controller to WebTracker.
The CEO of WebTracker, Mr. Bond, would like to assess the effectiveness of AmaZure's privacy controls, and he recently decided to hire you as an independent auditor. The scope of the engagement is limited only to the marketing services provided by WebTracker, you will not be evaluating any internal data processing activity, such as HR or Payroll.
This ad-hoc audit was triggered due to a future partnership between WebTracker and SmartHome — a partnership that will not require any data sharing. SmartHome is based in the USA, and most recently has dedicated substantial resources to developing smart refrigerators that can suggest the recommended daily calorie intake based on DNA information. This and other personal data is collected by WebTracker.
To get an idea of the scope of work involved, you have decided to start reviewing the company's documentation and interviewing key staff to understand potential privacy risks.
The results of this initial work include the following notes:
There are several typos in the current privacy notice of WebTracker, and you were not able to find the privacy notice for SmartHome.
You were unable to identify all the sub-processors working for SmartHome. No subcontractor is indicated in the cloud agreement with AmaZure, which is responsible for the support and maintenance of the cloud infrastructure.
There are data flows representing personal data being collected from the internal employees of WebTracker, including an interface from the HR system.
Part of the DNA data collected by WebTracker was from employees, as this was a prototype approved by the CEO of WebTracker.
All the WebTracker and SmartHome customers are based in USA and Canada.
Which of the following issues is most likely to require an investigation by the Chief Privacy Officer (CPO) of WebTracker?
A jurisdiction requiring an organization to place a link on the website that allows a consumer to opt-out of sharing is an example of what type of requirement?
Which of these is considered an ethical dark pattern on privacy?
What is the main reason a company relies on implied consent instead of explicit consent from a user to process her data?
What is the key idea behind the "flow" component of Nissenbaum's contextual integrity model?
Which of the following can be used to bypass even the best physical and logical security mechanisms to gain access to a system?
Which of the following entities would most likely be exempt from complying with the General Data Protection Regulation (GDPR)?
How should the sharing of information within an organization be documented?
SCENARIO
Please use the following to answer next question:
EnsureClaim is developing a mobile app platform for managing data used for assessing car accident insurance claims. Individuals use the app to take pictures at the crash site, eliminating the need for a built-in vehicle camera. EnsureClaim uses a third-party hosting provider to store data collected by the app. EnsureClaim customer service employees also receive and review app data before sharing with insurance claim adjusters.
The app collects the following information:
First and last name
Date of birth (DOB)
Mailing address
Email address
Car VIN number
Car model
License plate
Insurance card number
Photo
Vehicle diagnostics
Geolocation
What IT architecture would be most appropriate for this mobile platform?
An organization is reliant on temporary contractors for performing data analytics and they require access to personal data via software-as-a-service to perform their job. When the temporary contractor completes their work assignment, what woul^.be the most effective way to safeguard privacy and access to personal data when they leave?
A healthcare provider would like to data mine information for research purposes however the Chief Privacy Officer is concerned medical data of individuals may be disclosed overcome the concern, which is the preferred technique for protecting such data while still allowing for analysis?
What is the name of an alternative technique to counter the reduction in use of third-party cookies, where web publishers may consider utilizing data cached by a browser and returned with a subsequent request from the same resource to track unique users?
SCENARIO
Looking back at your first two years as the Director of Personal Information Protection and Compliance for the Berry Country Regional Medical Center in Thorn Bay, Ontario, Canada, you see a parade of accomplishments, from developing state-of-the-art simulation based training for employees on privacy protection to establishing an interactive medical records system that is accessible by patients as well as by the medical personnel. Now, however, a question you have put off looms large: how do we manage all the data-not only records produced recently, but those still on hand from years ago? A data flow diagram generated last year shows multiple servers, databases, and work stations, many of which hold files that have not yet been incorporated into the new records system. While most of this data is encrypted, its persistence may pose security and compliance concerns. The situation is further complicated by several long-term studies being conducted by the medical staff using patient information. Having recently reviewed the major Canadian privacy regulations, you want to make certain that the medical center is observing them.
You also recall a recent visit to the Records Storage Section, often termed “The Dungeon” in the basement of the old hospital next to the modern facility, where you noticed a multitude of paper records. Some of these were in crates marked by years, medical condition or alphabetically by patient name, while others were in undifferentiated bundles on shelves and on the floor. The back shelves of the section housed data tapes and old hard drives that were often unlabeled but appeared to be years old. On your way out of the dungeon, you noticed just ahead of you a small man in a lab coat who you did not recognize. He carried a batch of folders under his arm, apparently records he had removed from storage.
Which cryptographic standard would be most appropriate for protecting patient credit card information in the records system?
Which activity best supports the principle of data quality from a privacy perspective?
Which of the following is NOT a workplace surveillance best practice?
Which of the following is the most important action to take prior to collecting personal data directly from a customer?
After downloading and loading a mobile app, the user is presented with an account registration page requesting the user to provide certain personal details. Two statements are also displayed on the same page along with a box for the user to check to indicate their confirmation:
Statement 1 reads: “Please check this box to confirm you have read and accept the terms and conditions of the end user license agreement” and includes a hyperlink to the terms and conditions.
Statement 2 reads: “Please check this box to confirm you have read and understood the privacy notice” and includes a hyperlink to the privacy notice.
Under the General Data Protection Regulation (GDPR), what lawful basis would you primarily except the privacy notice to refer to?
Value sensitive design focuses on which of the following?
When analyzing user data, how is differential privacy applied?
SCENARIO
You have just been hired by Ancillary.com, a seller of accessories for everything under the sun, including waterproof stickers for pool floats and decorative bands and cases for sunglasses. The company sells cell phone cases, e-cigarette cases, wine spouts, hanging air fresheners for homes and automobiles, book ends, kitchen implements, visors and shields for computer screens, passport holders, gardening tools and lawn ornaments, and catalogs full of health and beauty products. The list seems endless. As the CEO likes to say, Ancillary offers, without doubt, the widest assortment of low-price consumer products from a single company anywhere.
Ancillary's operations are similarly diverse. The company originated with a team of sales consultants selling home and beauty products at small parties in the homes of customers, and this base business is still thriving. However, the company now sells online through retail sites designated for industries and demographics, sites such as “My Cool Ride" for automobile-related products or “Zoomer” for gear aimed toward young adults. The company organization includes a plethora of divisions, units and outrigger operations, as Ancillary has been built along a decentered model rewarding individual initiative and flexibility, while also acquiring key assets. The retail sites seem to all function differently, and you wonder about their compliance with regulations and industry standards. Providing tech support to these sites is also a challenge, partly due to a variety of logins and authentication protocols.
You have been asked to lead three important new projects at Ancillary:
The first is the personal data management and security component of a multi-faceted initiative to unify the company’s culture. For this project, you are considering using a series of third- party servers to provide company data and approved applications to employees.
The second project involves providing point of sales technology for the home sales force, allowing them to move beyond paper checks and manual credit card imprinting.
Finally, you are charged with developing privacy protections for a single web store housing all the company’s product lines as well as products from affiliates. This new omnibus site will be known, aptly, as “Under the Sun.” The Director of Marketing wants the site not only to sell Ancillary’s products, but to link to additional products from other retailers through paid advertisements. You need to brief the executive team of security concerns posed by this approach.
What technology is under consideration in the first project in this scenario?
A developer is designing a new system that allows an organization's helpdesk to remotely connect into the device of the individual to provide support Which of the following will be a privacy technologist's primary concern"?
SCENARIO
You have just been hired by Ancillary.com, a seller of accessories for everything under the sun, including waterproof stickers for pool floats and decorative bands and cases for sunglasses. The company sells cell phone cases, e-cigarette cases, wine spouts, hanging air fresheners for homes and automobiles, book ends, kitchen implements, visors and shields for computer screens, passport holders, gardening tools and lawn ornaments, and catalogs full of health and beauty products. The list seems endless. As the CEO likes to say, Ancillary offers, without doubt, the widest assortment of low-price consumer products from a single company anywhere.
Ancillary's operations are similarly diverse. The company originated with a team of sales consultants selling home and beauty products at small parties in the homes of customers, and this base business is still thriving. However, the company now sells online through retail sites designated for industries and demographics, sites such as “My Cool Ride" for automobile-related products or “Zoomer” for gear aimed toward young adults. The company organization includes a plethora of divisions, units and outrigger operations, as Ancillary has been built along a decentered model rewarding individual initiative and flexibility, while also acquiring key assets. The retail sites seem to all function differently, and you wonder about their compliance with regulations and industry standards. Providing tech support to these sites is also a challenge, partly due to a variety of logins and authentication protocols.
You have been asked to lead three important new projects at Ancillary:
The first is the personal data management and security component of a multi-faceted initiative to unify the company’s culture. For this project, you are considering using a series of third- party servers to provide company data and approved applications to employees.
The second project involves providing point of sales technology for the home sales force, allowing them to move beyond paper checks and manual credit card imprinting.
Finally, you are charged with developing privacy protections for a single web store housing all the company’s product lines as well as products from affiliates. This new omnibus site will be known, aptly, as “Under the Sun.” The Director of Marketing wants the site not only to sell Ancillary’s products, but to link to additional products from other retailers through paid advertisements. You need to brief the executive team of security concerns posed by this approach.
Which should be used to allow the home sales force to accept payments using smartphones?
SCENARIO
WebTracker Limited is a cloud-based online marketing service located in London. Last year, WebTracker migrated its IT infrastructure to the cloud provider AmaZure, which provides SQL Databases and Artificial Intelligence services to WebTracker. The roles and responsibilities between the two companies have been formalized in a standard contract, which includes allocating the role of data controller to WebTracker.
The CEO of WebTracker, Mr. Bond, would like to assess the effectiveness of AmaZure's privacy controls, and he recently decided to hire you as an independent auditor. The scope of the engagement is limited only to the marketing services provided by WebTracker, you will not be evaluating any internal data processing activity, such as HR or Payroll.
This ad-hoc audit was triggered due to a future partnership between WebTracker and SmartHome — a partnership that will not require any data sharing. SmartHome is based in the USA, and most recently has dedicated substantial resources to developing smart refrigerators that can suggest the recommended daily calorie intake based on DNA information. This and other personal data is collected by WebTracker.
To get an idea of the scope of work involved, you have decided to start reviewing the company's documentation and interviewing key staff to understand potential privacy risks.
The results of this initial work include the following notes:
There are several typos in the current privacy notice of WebTracker, and you were not able to find the privacy notice for SmartHome.
You were unable to identify all the sub-processors working for SmartHome. No subcontractor is indicated in the cloud agreement with AmaZure, which is responsible for the support and maintenance of the cloud infrastructure.
There are data flows representing personal data being collected from the internal employees of WebTracker, including an interface from the HR system.
Part of the DNA data collected by WebTracker was from employees, as this was a prototype approved by the CEO of WebTracker.
All the WebTracker and SmartHome customers are based in USA and Canada.
Based on the initial assessment and review of the available data flows, which of the following would be the most important privacy risk you should investigate first?
In order to prevent others from identifying an individual within a data set, privacy engineers use a cryptographically-secure hashing algorithm. Use of hashes in this way illustrates the privacy tactic known as what?
Which of these actions is NOT generally part of the responsibility of an IT or software engineer?
What is the main benefit of using a private cloud?
SCENARIO
Carol was a U.S.-based glassmaker who sold her work at art festivals. She kept things simple by only accepting cash and personal checks.
As business grew, Carol couldn't keep up with demand, and traveling to festivals became burdensome. Carol opened a small boutique and hired Sam to run it while she worked in the studio. Sam was a natural salesperson, and business doubled. Carol told Sam, “I don't know what you are doing, but keep doing it!"
But months later, the gift shop was in chaos. Carol realized that Sam needed help so she hired Jane, who had business expertise and could handle the back-office tasks. Sam would continue to focus on sales. Carol gave Jane a few weeks to get acquainted with the artisan craft business, and then scheduled a meeting for the three of them to discuss Jane's first impressions.
At the meeting, Carol could not wait to hear Jane's thoughts, but she was unprepared for what Jane had to say. “Carol, I know that he doesn't realize it, but some of Sam’s efforts to increase sales have put you in a vulnerable position. You are not protecting customers’ personal information like you should.”
Sam said, “I am protecting our information. I keep it in the safe with our bank deposit. It's only a list of customers’ names, addresses and phone numbers that I get from their checks before I deposit them. I contact them when you finish a piece that I think they would like. That's the only information I have! The only other thing I do is post photos and information about your work on the photo sharing site that I use with family and friends. I provide my email address and people send me their information if they want to see more of your work. Posting online really helps sales, Carol. In fact, the only complaint I hear is about having to come into the shop to make a purchase.”
Carol replied, “Jane, that doesn’t sound so bad. Could you just fix things and help us to post even more online?"
‘I can," said Jane. “But it's not quite that simple. I need to set up a new program to make sure that we follow the best practices in data management. And I am concerned for our customers. They should be able to manage how we use their personal information. We also should develop a social media strategy.”
Sam and Jane worked hard during the following year. One of the decisions they made was to contract with an outside vendor to manage online sales. At the end of the year, Carol shared some exciting news. “Sam and Jane, you have done such a great job that one of the biggest names in the glass business wants to buy us out! And Jane, they want to talk to you about merging all of our customer and vendor information with theirs beforehand."
What type of principles would be the best guide for Jane's ideas regarding a new data management program?
What is the term for information provided to a social network by a member?
Which of the following is considered a client-side IT risk?
Which of the following suggests the greatest degree of transparency?
Which of the following is one of the fundamental principles of information security?
of the following best describes a network threat model and Its uses?
What is true of providers of wireless technology?
A computer user navigates to a page on the Internet. The privacy notice pops up and the user clicks the box to accept cookies, then continues to scroll the page to read the Information displayed. This is an example of which type of consent?
An organization is concerned that its aging IT infrastructure will lead to Increased security and privacy risks. Which of the following would help mitigate these risks?
What risk is mitigated when routing meeting video traffic through a company’s application servers rather than sending the video traffic directly from one user to another?
When releasing aggregates, what must be performed to magnitude data to ensure privacy?
Which of the following is NOT a valid basis for data retention?
A credit card with the last few numbers visible is an example of what?
Which of the following would be the best method of ensuring that Information Technology projects follow Privacy by Design (PbD) principles?
Which of the following are the mandatory pieces of information to be included in the documentation of records of processing activities for an organization that processes personal data on behalf of another organization?
What is an example of a just-in-time notice?
You are a wine collector who uses the web to do research about your hobby. You navigate to a news site and an ad for wine pops up. What kind of advertising is this?
Which of the following is NOT a step in the methodology of a privacy risk framework?
Not updating software for a system that processes human resources data with the latest security patches may create what?
Which is NOT a suitable method for assuring the quality of data collected by a third-party company?
What is the main function of the Amnesic Incognito Live System or TAILS device?
An organization is launching a smart watch which, in addition to alerts, will notify the the wearer of incoming calls allowing them to answer on the device. This convenience also comes with privacy concerns and is an example of?
SCENARIO
Wesley Energy has finally made its move, acquiring the venerable oil and gas exploration firm Lancelot from its long-time owner David Wilson. As a member of the transition team, you have come to realize that Wilson's quirky nature affected even Lancelot's data practices, which are maddeningly inconsistent. “The old man hired and fired IT people like he was changing his necktie,” one of Wilson’s seasoned lieutenants tells you, as you identify the traces of initiatives left half complete.
For instance, while some proprietary data and personal information on clients and employees is encrypted, other sensitive information, including health information from surveillance testing of employees for toxic exposures, remains unencrypted, particularly when included within longer records with less-sensitive data. You also find that data is scattered across applications, servers and facilities in a manner that at first glance seems almost random.
Among your preliminary findings of the condition of data at Lancelot are the following:
Cloud technology is supplied by vendors around the world, including firms that you have not heard of. You are told by a former Lancelot employee that these vendors operate with divergent security requirements and protocols.
The company’s proprietary recovery process for shale oil is stored on servers among a variety of less-sensitive information that can be accessed not only by scientists, but by personnel of all types at most company locations.
DES is the strongest encryption algorithm currently used for any file.
Several company facilities lack physical security controls, beyond visitor check-in, which familiar vendors often bypass.
Fixing all of this will take work, but first you need to grasp the scope of the mess and formulate a plan of action to address it.
Which procedure should be employed to identify the types and locations of data held by Wesley Energy?
Which of the following CANNOT be effectively determined during a code audit?