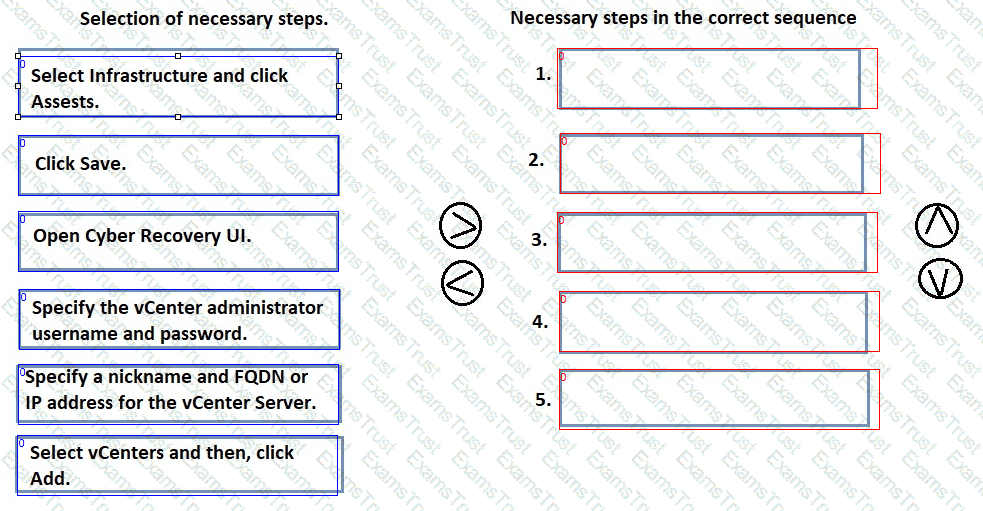
DRAG DROP
When you install a vCenter Server in an on-premises Dell PowerProtect Cyber Recovery vault, you must register it with the PowerProtect Cyber Recovery software. Arrange the necessary steps in chronological order.
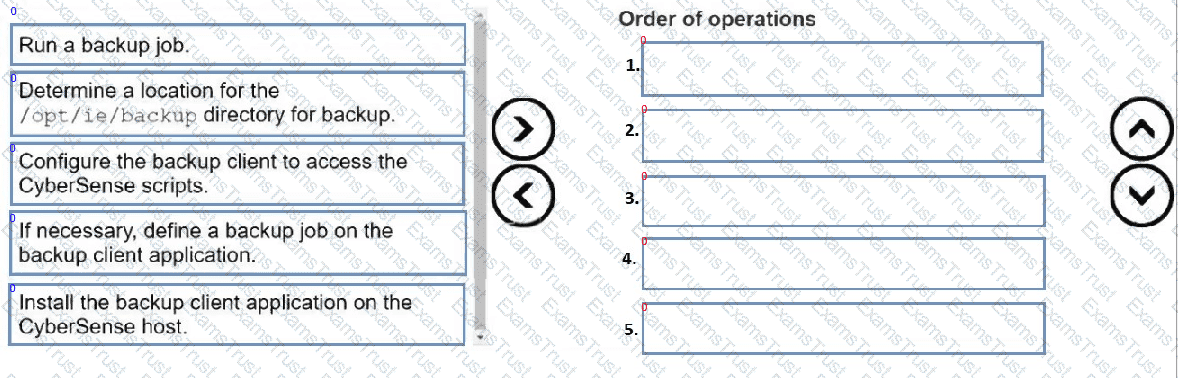
DRAG DROP
Put the following steps in the correct order to back up the Index Engines CyberSense configuration files:
Which is the best practice when securing PowerProtect Data Domain in Dell PowerProtect Cyber Recovery vault?
You execute the crsetup.sh --check command to upgrade the Dell PowerProtect Cyber Recovery software using the precheck option.
What is the first check that the update precheck performs?
A customer deploying Dell PowerProtect Cyber Recovery software on Microsoft Azure.
Which two components does the ARM template create? (Choose two.)
What is used to confirm the CyberSense Server is ready for software install?
An IT manager needs to rerun a previously generated Dell PowerProtect Cyber Recovery report to verify the job activities for a specific period. They want to ensure that report includes the latest data.
What action should the IT manager take to rerun the report?
Which common cyber-attack overwhelms the resources of the system with excessive requests that consume all the resources to bring it down?
What does Dell Technologies recommend before defining Dell PowerProtect Cyber Recovery policies?
What are the two types of alerts in the CyberSense Alerts dashboard? (Choose two.)
What is a key technological limitation that warrants the use of an air-gapped vault in dell PowerProtect Cyber Recovery?