You find one of your cluster gateways showing “Down” when you run the “cphaprob stat” command. You then run the “clusterXL_admin up” on the down member but unfortunately the member continues to show down. What command do you run to determine the cause?
Which of the following describes how Threat Extraction functions?
Which one of the following is true about Threat Extraction?
Which configuration file contains the structure of the Security Server showing the port numbers, corresponding protocol name, and status?
What is the most recommended way to install patches and hotfixes?
What is a best practice before starting to troubleshoot using the “fw monitor” tool?
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Wire Mode configuration, chain modules marked with ____________ will not apply.
From SecureXL perspective, what are the tree paths of traffic flow:
Where do you create and modify the Mobile Access policy in R81?
Security Checkup Summary can be easily conducted within:
When setting up an externally managed log server, what is one item that will not be configured on the R81 Security Management Server?
What is the port used for SmartConsole to connect to the Security Management Server?
What is the name of the secure application for Mail/Calendar for mobile devices?
Traffic from source 192.168.1.1 is going to The Application Control Blade on the gateway is inspecting the traffic. Assuming acceleration is enabled which path is handling the traffic?
To accelerate the rate of connection establishment, SecureXL groups all connection that match a particular service and whose sole differentiating element is the source port. The type of grouping enables even the very first packets of a TCP handshake to be accelerated. The first packets of the first connection on the same service will be forwarded to the Firewall kernel which will then create a template of the connection. Which of the these is NOT a SecureXL template?
What is considered Hybrid Emulation Mode?
What is mandatory for ClusterXL to work properly?
Which of these is an implicit MEP option?
When an encrypted packet is decrypted, where does this happen?
Customer’s R81 management server needs to be upgraded to R81.20. What is the best upgrade method when the management server is not connected to the Internet?
What is the main difference between Threat Extraction and Threat Emulation?
What are the blades of Threat Prevention?
Which GUI client is supported in R81?
Which command shows detailed information about VPN tunnels?
What component of R81 Management is used for indexing?
Which of the following links will take you to the SmartView web application?
SmartEvent has several components that function together to track security threats. What is the function of the Correlation Unit as a component of this architecture?
Which Check Point daemon monitors the other daemons?
To enable Dynamic Dispatch on Security Gateway without the Firewall Priority Queues, run the following command in Expert mode and reboot:
How often does Threat Emulation download packages by default?
How would you deploy TE250X Check Point appliance just for email traffic and in-line mode without a Check Point Security Gateway?
NO: 180
What command can you use to have cpinfo display all installed hotfixes?
The Correlation Unit performs all but the following actions:
What information is NOT collected from a Security Gateway in a Cpinfo?
Which of the following is NOT a type of Check Point API available in R81.x?
After making modifications to the $CVPNDIR/conf/cvpnd.C file, how would you restart the daemon?
When gathering information about a gateway using CPINFO, what information is included or excluded when using the “-x” parameter?
What is the command to see cluster status in cli expert mode?
What is the purpose of a SmartEvent Correlation Unit?
Which of the following will NOT affect acceleration?
The following command is used to verify the CPUSE version:
You are investigating issues with to gateway cluster members are not able to establish the first initial cluster synchronization. What service is used by the FWD daemon to do a Full Synchronization?
How do you enable virtual mac (VMAC) on-the-fly on a cluster member?
When installing a dedicated R81 SmartEvent server. What is the recommended size of the root partition?
Which Check Point software blades could be enforced under Threat Prevention profile using Check Point R81.20 SmartConsole application?
Which command gives us a perspective of the number of kernel tables?
Which directory below contains log files?
What are the two ClusterXL Deployment options?
SmartEvent uses it's event policy to identify events. How can this be customized?
Which Check Point process provides logging services, such as forwarding logs from Gateway to Log Server, providing Log Export API (LEA) & Event Logging API (EL-A) services.
What CLI utility runs connectivity tests from a Security Gateway to an AD domain controller?
Which process handles connection from SmartConsole R81?
How does the Anti-Virus feature of the Threat Prevention policy block traffic from infected websites?
What is false regarding prerequisites for the Central Deployment usage?
When Configuring Endpoint Compliance Settings for Applications and Gateways within Mobile Access, which of the three approaches will allow you to configure individual policies for each application?
Which of the following is NOT a component of a Distinguished Name?
Which is the command to identify the NIC driver before considering about the employment of the Multi-Queue feature?
When configuring SmartEvent Initial settings, you must specify a basic topology for SmartEvent to help it calculate traffic direction for events. What is this setting called and what are you defining?
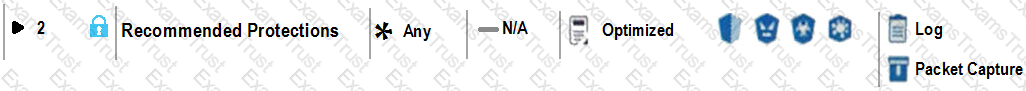
View the rule below. What does the lock-symbol in the left column mean? (Choose the BEST answer.)
Which command is used to add users to or from existing roles?
What are valid authentication methods for mutual authenticating the VPN gateways?
What kind of information would you expect to see when using the "sim affinity -I" command?
SandBlast agent extends 0-day prevention to what part of the network?
According to the policy installation flow the transfer state (CPTA) is responsible for the code generated by the FWM. On the Security Gateway side a process receives them and first stores them Into a temporary directory. Which process is true for receiving these Tiles;
Which of the following is NOT an attribute of packet acceleration?
An established connection is going to The Application Control Blade Is inspecting the traffic. If SecureXL and CoreXL are both enabled, which path is handling the traffic?
The “MAC magic” value must be modified under the following condition:
Which command collects diagnostic data for analyzing a customer setup remotely?
What ports are used for SmartConsole to connect to the Security Management Server?
Which software blade does NOT accompany the Threat Prevention policy?
At what point is the Internal Certificate Authority (ICA) created?
You need to change the MAC-address on eth2 interface of the gateway. What command and what mode will you use to achieve this goal?
What are the two modes for SNX (SSL Network Extender)?
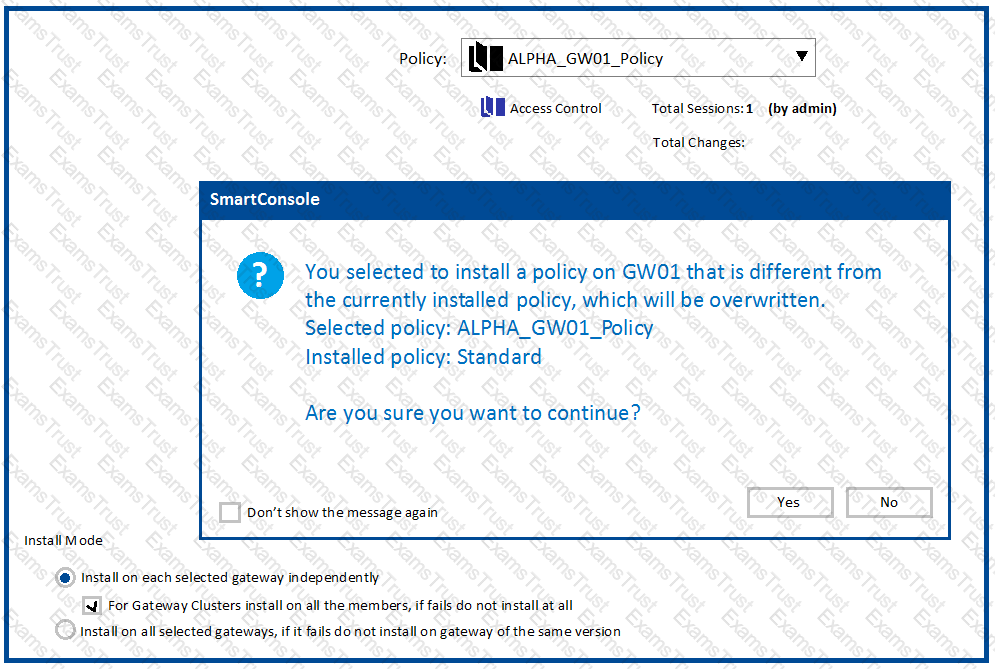
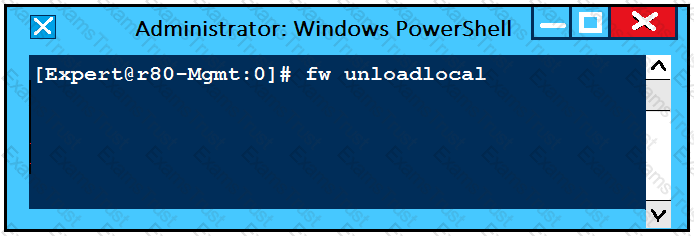
You have pushed policy to GW-3 and now cannot pass traffic through the gateway. As a last resort, to restore traffic flow, what command would you run to remove the latest policy from GW-3?
Which command is used to obtain the configuration lock in Gaia?
What two ordered layers make up the Access Control Policy Layer?
In which scenario will an administrator need to manually define Proxy ARP?
What is the correct Syntax for adding an access-rule via R80 API?
Why would an administrator see the message below?
Aaron is a Syber Security Engineer working for Global Law Firm with large scale deployment of Check Point Enterprise Appliances running GAiA R81.X The Network Security Developer Team is having an issue testing the API with a newly deployed R81.X Security Management Server Aaron wants to confirm API services are working properly. What should he do first?
In which deployment is the security management server and Security Gateway installed on the same appliance?
How can you switch the active log file?
An administrator wishes to enable Identity Awareness on the Check Point firewalls. However, they allow users to use company issued or personal laptops. Since the administrator cannot manage the personal laptops, which of the following methods would BEST suit this company?
What are the two high availability modes?
You want to allow your Mobile Access Users to connect to an internal file share. Adding the Mobile Application 'File Share' to your Access Control Policy in the SmartConsole didn't work. You will be only allowed to select Services for the 'Service & Application' column How to fix it?
Which Mobile Access Solution is clientless?
You work as a security administrator for a large company. CSO of your company has attended a security conference where he has learnt how hackers constantly modify their strategies and techniques to evade detection and reach corporate resources. He wants to make sure that his company has the tight protections in place. Check Point has been selected for the security vendor.
Which Check Point product protects BEST against malware and zero-day attacks while ensuring quick delivery of safe content to your users?
What is the recommended way to have a redundant Sync connection between the cluster nodes?
Hit Count is a feature to track the number of connections that each rule matches, which one is not benefit of Hit Count.
In Advanced Permanent Tunnel Configuration, to set the amount of time the tunnel test runs without a
response before the peer host is declared ‘down’, you would set the_________?
Matt wants to upgrade his old Security Management server to R81.x using the Advanced Upgrade with Database Migration. What is one of the requirements for a successful upgrade?
Which of the following blades is NOT subscription-based and therefore does not have to be renewed on a regular basis?
After finishing installation admin John likes to use top command in expert mode. John has to set the expert-password and was able to use top command. A week later John has to use the top command again, He detected that the expert password is no longer valid. What is the most probable reason for this behavior?
Which 3 types of tracking are available for Threat Prevention Policy?
Check Point recommends configuring Disk Space Management parameters to delete old log entries when available disk space is less than or equal to?
Where you can see and search records of action done by R81 SmartConsole administrators?
In R81 spoofing is defined as a method of:
SandBlast Mobile identifies threats in mobile devices by using on-device, network, and cloud-based algorithms and has four dedicated components that constantly work together to protect mobile devices and their data. Which component is NOT part of the SandBlast Mobile solution?
Check Pont Central Deployment Tool (CDT) communicates with the Security Gateway / Cluster Members over Check Point SIC _______ .
Which TCP-port does CPM process listen to?
Tom has been tasked to install Check Point R81 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
What Factor preclude Secure XL Templating?
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidated management console. It empowers the migration from legacy Client-side logic to Server-side logic. The cpm process:
Which command can you use to verify the number of active concurrent connections?
To fully enable Dynamic Dispatcher with Firewall Priority Queues on a Security Gateway, run the following command in Expert mode then reboot:
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidates management console. CPM allows the GUI client and management server to communicate via web services using ___________.
Which command collects diagnostic data for analyzing customer setup remotely?
In a Client to Server scenario, which inspection point is the first point immediately following the tables and rule base check of a packet coming from outside of the network?
Session unique identifiers are passed to the web api using which http header option?
Fill in the blank: The tool _____ generates a R81 Security Gateway configuration report.
You can select the file types that are sent for emulation for all the Threat Prevention profiles. Each profile defines a(n) _____ or _____ action for the file types.
Which command shows actual allowed connections in state table?
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
What is a feature that enables VPN connections to successfully maintain a private and secure VPN session without employing Stateful Inspection?
Sticky Decision Function (SDF) is required to prevent which of the following? Assume you set up an Active-Active cluster.
Which of these statements describes the Check Point ThreatCloud?
Which view is NOT a valid CPVIEW view?
What are the different command sources that allow you to communicate with the API server?
CPM process stores objects, policies, users, administrators, licenses and management data in a database. The database is:
What is the difference between an event and a log?
fwssd is a child process of which of the following Check Point daemons?
What SmartEvent component creates events?
What is the least amount of CPU cores required to enable CoreXL?
Full synchronization between cluster members is handled by Firewall Kernel. Which port is used for this?
In order to get info about assignment (FW, SND) of all CPUs in your SGW, what is the most accurate CLI command?
Which of the following Check Point processes within the Security Management Server is responsible for the receiving of log records from Security Gateway?
What is not a component of Check Point SandBlast?
The Firewall kernel is replicated multiple times, therefore:
Which of the following type of authentication on Mobile Access can NOT be used as the first authentication method?
The Firewall Administrator is required to create 100 new host objects with different IP addresses. What API command can he use in the script to achieve the requirement?
NAT rules are prioritized in which order?
1. Automatic Static NAT
2. Automatic Hide NAT
3. Manual/Pre-Automatic NAT
4. Post-Automatic/Manual NAT rules
Which packet info is ignored with Session Rate Acceleration?
Connections to the Check Point R81 Web API use what protocol?
What happen when IPS profile is set in Detect Only Mode for troubleshooting?
What is the limitation of employing Sticky Decision Function?
R81.20 management server can manage gateways with which versions installed?
You want to gather and analyze threats to your mobile device. It has to be a lightweight app. Which application would you use?
Fill in the blank: The R81 feature _____ permits blocking specific IP addresses for a specified time period.
There are 4 ways to use the Management API for creating host object with R81 Management API. Which one is NOT correct?
In R81, how do you manage your Mobile Access Policy?
When requiring certificates for mobile devices, make sure the authentication method is set to one of the following, Username and Password, RADIUS or ________.
For best practices, what is the recommended time for automatic unlocking of locked admin accounts?
What will be the effect of running the following command on the Security Management Server?
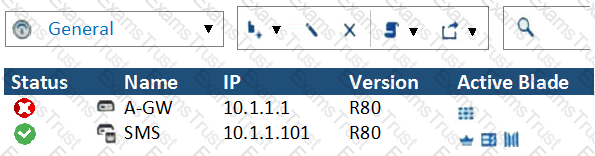
What does it mean if Deyra sees the gateway status? (Choose the BEST answer.)
Which of the following is NOT a VPN routing option available in a star community?
SmartEvent provides a convenient way to run common command line executables that can assist in investigating events. Right-clicking the IP address, source or destination, in an event provides a list of default and customized commands. They appear only on cells that refer to IP addresses because the IP address of the active cell is used as the destination of the command when run. The default commands are:
What kind of information would you expect to see using the sim affinity command?
What is correct statement about Security Gateway and Security Management Server failover in Check Point R81.X in terms of Check Point Redundancy driven solution?
What is the order of NAT priorities?
What command would show the API server status?
On what port does the CPM process run?
Which NAT rules are prioritized first?
Vanessa is firewall administrator in her company. Her company is using Check Point firewall on a central and several remote locations which are managed centrally by R77.30 Security Management Server. On central location is installed R77.30 Gateway on Open server. Remote locations are using Check Point UTM-1570 series appliances with R75.30 and some of them are using a UTM-1-Edge-X or Edge-W with latest available firmware. She is in process of migrating to R81.
What can cause Vanessa unnecessary problems, if she didn’t check all requirements for migration to R81?
Fill in the blank: The “fw monitor” tool can be best used to troubleshoot ____________________.
How many layers make up the TCP/IP model?
You need to change the number of firewall Instances used by CoreXL. How can you achieve this goal?
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
What CLI command compiles and installs a Security Policy on the target’s Security Gateways?
When deploying SandBlast, how would a Threat Emulation appliance benefit from the integration of ThreatCloud?
What is the responsibility of SOLR process on R81.20 management server?
In the Firewall chain mode FFF refers to:
In the Check Point Firewall Kernel Module, each Kernel is associated with a key, which specifies the type of traffic applicable to the chain module. For Stateful Mode configuration, chain modules marked with __________________ will not apply.
Which SmartConsole tab is used to monitor network and security performance?
In Logging and Monitoring, the tracking options are Log, Detailed Log and Extended Log. Which of the following options can you add to each Log, Detailed Log and Extended Log?
Which Check Point feature enables application scanning and the detection?
Which of the following commands shows the status of processes?
During the Check Point Stateful Inspection Process, for packets that do not pass Firewall Kernel Inspection and are rejected by the rule definition, packets are:
In ClusterXL Load Sharing Multicast Mode:
When using CPSTAT, what is the default port used by the AMON server?
What must you do first if “fwm sic_reset” could not be completed?
What key is used to save the current CPView page in a filename format cpview_”cpview process ID”.cap”number of captures”?
What statement best describes the Proxy ARP feature for Manual NAT in R81.20?
Which application should you use to install a contract file?
Which file contains the host address to be published, the MAC address that needs to be associated with the IP Address, and the unique IP of the interface that responds to ARP request?
The SmartEvent R81 Web application for real-time event monitoring is called:
What are the types of Software Containers?
Capsule Connect and Capsule Workspace both offer secured connection for remote users who are using their mobile devices. However, there are differences between the two.
Which of the following statements correctly identify each product's capabilities?
What is UserCheck?
You notice that your firewall is under a DDoS attack and would like to enable the Penalty Box feature, which command you use?
With SecureXL enabled, accelerated packets will pass through the following:
After the initial installation on Check Point appliance, you notice that the Management-interface and default gateway are incorrect.
Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
How many policy layers do Access Control policy support?
Check Point APIs allow system engineers and developers to make changes to their organization’s security policy with CLI tools and Web Services for all the following except:
You want to verify if your management server is ready to upgrade to R81.20. What tool could you use in this process?
What is the recommended number of physical network interfaces in a Mobile Access cluster deployment?
Which is NOT a SmartEvent component?
Joey wants to upgrade from R75.40 to R81 version of Security management. He will use Advanced Upgrade with Database Migration method to achieve this.
What is one of the requirements for his success?
Which path below is available only when CoreXL is enabled?